

Diagnosis Date: 2026/02/25 16:40
Method: Detailed Diagnosis
Number of Reports
16
Last Update:
By GMO Cybersecurity by Ierae, Inc.
ASM is Myanmar's first premium cloud-based security solution. It empowers organizations to proactively identify and manage external IT assets—including websites and networks—to neutralize vulnerabilities before they can be exploited.


These are common security headaches — and our solution fixes all of them.

Risk of forgotten or "ghost" websites and servers operating online without IT team monitoring.

Managing a fast-growing environment where new subdomains, cloud instances, and IP addresses are constantly added.

Inadequate security scan frequency (e.g., annual scans) leading to critical bugs remaining undetected for months.

Uncertainty regarding whether external vendors or partners maintaining network connections adhere to required security standards.

Potential for accidental exposure of databases or ports to the public internet due to configuration mistakes.

Requirement to provide auditors or stakeholders with proof of continuous visibility and control over the entire external network.

Insufficient insight into how the network appears to a hacker, despite having internal security checks in place.
Every organization has digital assets that could be at risk — and most don't even realize it. The good news? You can find out in minutes, not months.
Just by registering a domain or spinning up a server, your organization already has an attack surface — whether you manage it or not.
Setting up a website or connecting network devices is easy. But without proper oversight, these assets can quickly become vulnerable entry points.
Even if your infrastructure feels fragile or exposed, our platform identifies every weakness — so you can fix what matters before attackers find it.
You don't need a dedicated security team to get started. Register your domains and IPs, and our system handles the rest — scanning, analyzing, and delivering clear, actionable insights you can act on right away.
Choose the plan that fits your organization's security needs.
For Individual Use
For small teams getting started.
For growing businesses.
For teams needing full coverage.
For large organizations.
Advanced tools and capabilities designed to identify, assess, and mitigate cyber threats across your entire digital ecosystem.
Discover and catalog all publicly accessible IT assets across your entire organization.
Monitor for leaked IDs and passwords on the dark web to prevent unauthorized access.
Scan the range of remote access without affecting the target systems or infrastructure.
Active scanning without affecting the target for thorough vulnerability identification.
Manage your list of devices and vulnerabilities from a single centralized dashboard.
Expert consultation and recommendations to strengthen your overall security posture.
Comprehensive security reports generated on a regular basis with actionable insights.
Systematic risk assessment and management to keep your organization protected.
Instant email notifications when critical vulnerabilities or threats are detected.
A systematic approach to managing your attack surface from discovery to response.
GMO Cybersecurity by Ierae's white hat hackers will identify your company's exposed IT assets (shadow IT) from an attacker's perspective.
Automated weekly scans identify vulnerabilities. On-demand scans are also available.
Follow the instructions in the tool. If you have any questions, our security consultants will assist you!
The tool automatically ranks vulnerabilities based on their impact, and security consultants provide advice on prioritization.
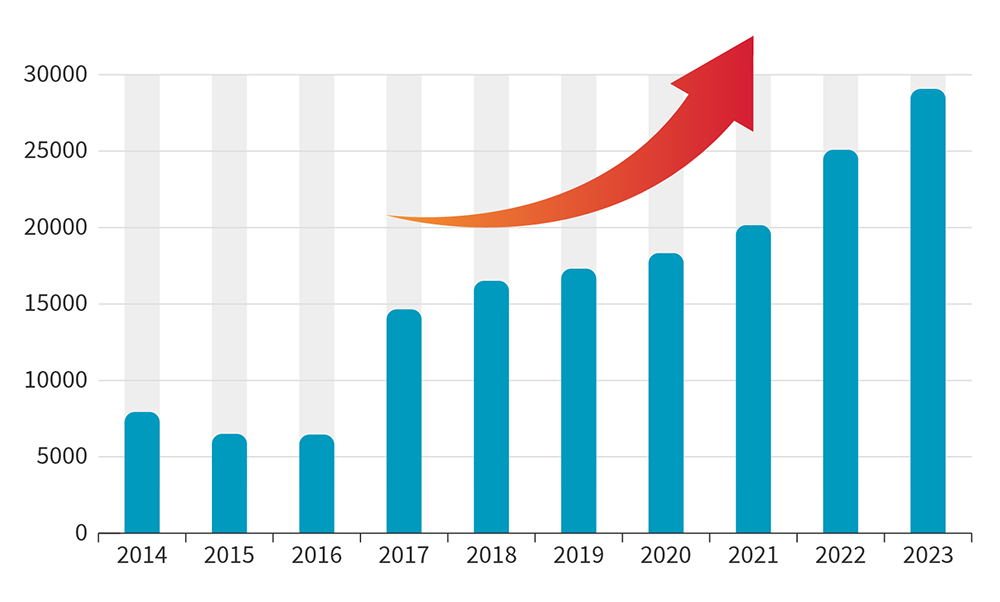
Cyber threats are growing rapidly. Proactive management of your attack surface is no longer optional.
Internal IT assets can become externally exposed due to misconfiguration or cloud deployment, creating unknown entry points.
Publicly accessible systems like VPNs, websites, and routers are top targets for cyberattackers seeking unauthorized access.
System modifications and updates continuously introduce new vulnerabilities, requiring regular checkups and proactive management.
Registered vulnerabilities are increasing year by year, making continuous monitoring critical.
Attack surface management tools and consulting — anyone can easily achieve ASM.

Comprehensive security testing to identify SQL injection, XSS, CSRF, and other OWASP Top 10 threats.

Deep analysis to detect misconfigurations, open ports, vulnerable services, and potential entry points.

Specialized scanning for WordPress, Drupal, and Joomla to identify plugin vulnerabilities and misconfigurations.
Comprehensive security reports with clear risk grading, vulnerability breakdowns, and actionable remediation guidance for every domain.
Last scan: March 14, 2026 at 19:10
* This is a simulated interface for illustration purposes. Actual reports may vary in layout and detail.
Powered by the world's leading white hat hackers with decades of combined security expertise.
A complete, end-to-end solution for cyberattack prevention, detection, and response.
Flexibly designed for all types of users — from small businesses to large enterprises.
Bringing simple, easy-to-use security to everyone.
Our ASM tool was developed to ensure that anyone can use it easily with just a few steps.
Everything you need to know about our Attack Surface Management solution.
Attack Surface Management is the process of discovering, analyzing, and assessing all externally exposed digital assets such as domains, IPs, web applications, and network equipment. It helps organizations identify vulnerabilities and security gaps before attackers can exploit them.
The main difference is the number of domains you can assess. ASM-S supports up to 10 domains, ASM-M up to 30, ASM-L up to 50, and ASM-XL up to 100 domains. All plans include the same core features: 189 assessment items, unlimited scans, network assessment, web app assessment, and PDF report export.
Every plan includes 189 individual security checks that cover a wide range of vulnerabilities and misconfigurations. These items span across network infrastructure, web application security, SSL/TLS configuration, DNS settings, open ports, outdated software, and more — giving you a thorough diagnosis of your attack surface.
All plans come with unlimited scans, meaning you can run as many assessments as you need throughout your subscription period. There are no caps or extra charges per scan — run them whenever you want to check for new vulnerabilities or verify that issues have been resolved.
Network Assessment scans your infrastructure for open ports, vulnerable services, misconfigurations, and potential entry points. Web App Assessment checks your web applications for common threats like SQL injection, XSS, CSRF, and other OWASP Top 10 vulnerabilities. Both are included in every plan.
Yes. Every plan includes PDF report export so you can download and share your assessment results with your team, management, or auditors. Reports include detailed findings, risk ratings, and remediation recommendations in a clear, professional format.
Simply count how many domains your organization needs to assess. If you have up to 10 domains, ASM-S is a great fit. For 30 domains, go with ASM-M. Larger organizations with up to 50 or 100 domains should choose ASM-L or ASM-XL respectively. Not sure? Contact us and we'll help you find the right plan.
Getting started is simple. Choose the plan that matches your domain count, click "Contact Us," and fill in your details. Our team will reach out within 3 business days and provide you with your account information so you can log in and start assessing your attack surface.